Now quoting myself  , because after @grb 's post, I wanted to explain what I was aiming at here.
, because after @grb 's post, I wanted to explain what I was aiming at here.
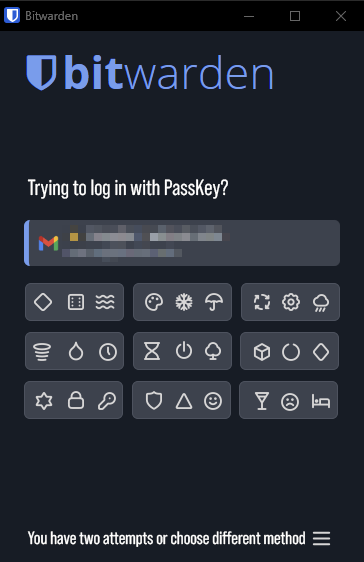
Apart from the question “UV or not UV in Bitwarden” (of course it’s more complex than that, as e.g. @FineWolf expressed recently, but that’s the offending object) or “which future form of UV may be more user-friendly”, I would suggest, maybe viewing UV from a different point of view (though I can understand everyone’s frustration with the current/former implementation in Bitwarden):
First case: you don’t store your TOTP seeds in Bitwarden because of security reasons.
In this case, you (theoretically) wouldn’t want to store any passkeys in Bitwarden without user verification, as it would be the same as having stored your passwords + TOTP seeds in Bitwarden. Because any passkey in Bitwarden would make it possible to login to a service without additional 2FA/MFA.
In this case - at least I understand it like this - only having UV (but implemented in a user-friendly manner!) would allow such a security-cautious person to store and use passkeys in Bitwarden at all.
Second case: you do store your TOTP seeds in Bitwarden because it is more convenient.
In this case, you at least don’t see a problem in storing your passkeys in Bitwarden (as it equals storing your passwords and TOTP seeds alongside in Bitwarden). And using a passkey replaces using (additional to the passwords) TOTP codes or other forms of 2FA/MFA. Therefore, with passkey-UV, you get a new form of user-friction - okay, point taken. But at the same time you (possibly / for most services - there are always exceptions) get rid of the old inconvenience of using TOTP codes or other forms of 2FA/MFA, because it is now “contained” in the passkey and it’s UV.
In a way, you would be replacing your TOTP codes / other forms of 2FA/MFA with the UV of the passkey. (and have the additional advantage of having a phishing-resistant login method)
(Maybe unfair  but of course - this advantage of getting rid of other 2FA-/MFA-inconveniences would be true also for those, who don’t store their TOTP codes/seeds in Bitwarden (or use other forms of 2FA/MFA) by using passkey + UV with Bitwarden…))
but of course - this advantage of getting rid of other 2FA-/MFA-inconveniences would be true also for those, who don’t store their TOTP codes/seeds in Bitwarden (or use other forms of 2FA/MFA) by using passkey + UV with Bitwarden…))
So regardless of how you have done it before (stored TOTP codes or didn’t store TOTP codes in Bitwarden) - it’s maybe not that bad of a change, having user-friendly UV with Bitwarden’s passkeys.
Maybe not the “solution” you are looking for… But maybe at least consider, if a more user-friendly UV than we experienced this last month with Bitwarden is not that bad in the long run - and helps get rid of other inconveniences (having to open your mobile phone, searching for TOTP codes… or other 2FA/MFA).
BTW, in a way - as I understand it - the UV can be seen as the MFA-part of a passkey. So in general, without UV, the passkeys in Bitwarden would lose their 2FA/MFA-quality. So at least, I guess I want to say, don’t see UV only as an inconvenience, as it has it’s general purpose per design…
I’m looking forward to possible answers from others about possible attack vectors. I just want to add my understanding of the UV in general: in the passkey-design, the UV is a very powerful mechanism, as I understand it, as it allows (or disallows) access to the private key to answer the challenge from the relying party. So the UV ultimately protects the private key, so to say. So the UV is not a trivial part of the passkey authentication process, but a part of the security architecture (and as written in the paragraph above, it’s more or less the 2FA/MFA-feature of a passkey, if I understand it correctly).