Make it so once the 2fa is used to login to one account it won’t accept the same code on another login attempt whether it be for logging into vault or accessing individual user & pass details. eg. I try to login and use my 2fa app code to login to browser version the hacker uses it to do the same except he steals every single password in the database without this implementation. The reason to do this is to try and mitigate keyloggers/singular 2fa code compromised situations.
A post was split to a new topic: Immediate Logout is not immediate
@paranoisetsin13 Welcome to the forum!
TOTP is a one-time password, and the RFC (last paragraph of section 5.2) specifies that
Thus, the RFC for the TOTP protocol specifies that when you have successfully completed the 2FA authorization process for logging in to you account, an attacker with knowledge of the TOTP code will not be able to re-use that code.
Do you have any evidence that Bitwarden’s 2FA is not adhering to the RFC specifications?
If your device is infected by malware capable of installing a keylogger, then the malware is already able to read all of your vault contents directly from the process memory, no matter what method is used to log in to or unlock the Bitwarden app.
It is your responsibility to ensure that devices on which you have installed Bitwarden are not compromised.
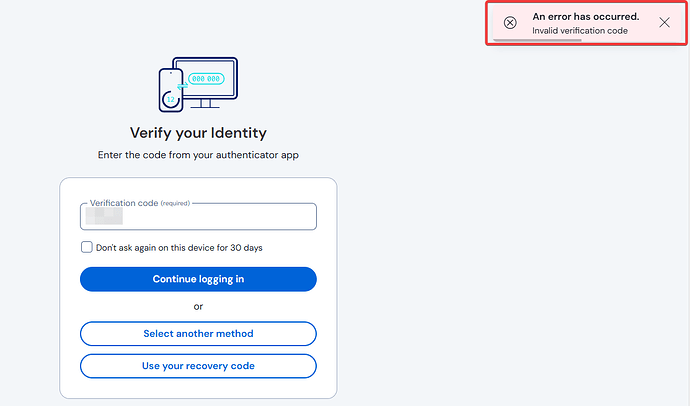
I logged into the vault using an app on an alternate phone and a browser on a pc using the same 2fa code from Authy. I was able to gain entry with the same code after already using it.
If 2fa was enabled at the per password/ secure object level would someone still see unencrypted passwords/notes in memory?