I’d like to save the Strong Password Generator | Bitwarden page to my thumbdrive, and then be able to use it completely offline. Is that possible? Thanks in advance.
this would work when they complete the offline version of Bitwarden.
You can install Bitwarden’s Portable Desktop app on a USB, then launch the portable app while disconnected from the internet, and use the Password Generator tool there.
If you want a simper solution, there are other password/passphrase generators available that can be downloaded for off-line use (from sources other than Bitwarden). Here is one that I like:
https://passhelp.github.io/generator/
Just right-click in the page and choose Save As to save locally as an .html file, which you will then be able to open while off-line.
If you want a wider selection, check out Aaron Toponce’s “audited” password/passphrase generator list, and choose among those that have a value of “Client” in the “Generator” column (this means that the passwords are generated client-side):
Thank you very much! Great list! I was liking the idea of Zeck’s readable passwords, but got scared when I saw, but don’t quite understand, the reportedly weak math.random() call. Readable Passphrase JS Demo That fear sent me back to BitWarden, whom I trust, but that didn’t work offline. Thanks again!
Just some random notes from a random novice:
If one needed 128 bits for some purpose (convenient source for testing only: RANDOM.ORG - Integer Generator)
then paste those 128 random 0s and 1s into
Password Strength Tester?
The output is:
Password Length: 128
Charsetsize: 10
ShannonEntropyBits: 127.91 <— goal
TrigraphEntropyBits: 404.96
Strength Code: Very Strong
All Possible combinations: 1e+128
[Time Required to Exhaustively Search All Possible Combinations]
Custom Scenario: Guesses Per Second Not Specified.
GRC.com Online Attack Example Scenario: 3.170979198376459e+117 years
Password-Depot.de Example Scenario: 1.5854895991882295e+111 years
GRC.com Offline Fast Attack Example Scenario: 3.1709791983764588e+109 years
Distributed.net May 8, 2012 Scenario: 3.9637239979705735e+108 years
GRC.com Massive Cracking Array Example: 3.1709791983764586e+106 years
So, the ShannonEntropyBits is the goal to compare the strength of 128 0s and 1s to a memorable word passphrase, vs TrigraphEntropyBits).
Example 4-word passphrase from the little password helper
pillar-handicap-knickers-justice
Password Length: 32
Charsetsize: 58
ShannonEntropyBits: 123.74 ← pretty darn good
TrigraphEntropyBits: 181.24
add a couple of character types, and importantly, length:
pillar-handicap-knickers-justiceE4
Password Length: 34
Charsetsize: 94
ShannonEntropyBits: 136.71 ← unequivocal
TrigraphEntropyBits: 215.64
Looks like 4 words and a couple of added character types is a memorable win. Length should probably be > 32 characters. As-is, use at your own risk.
Can someone help me prove, perhaps using browser dev tools breakpoints?, that this tool
https://passhelp.github.io/generator/
(or any tool) doesn’t hit the Math.random() functions? Examples found using Search in dev tools:
const a = Math.random().toString().slice(4);
const r = Math.random().toString().slice(4);
const s = Math.random().toString().slice(4);
@pjalajas I don’t know what file your Dev Tools search is looking in. I found nothing of the sort in the HTML code (view by pressing Ctrl+U while the Little Password Helper page is open in your browser).
If you trust Aaron Toponce’s work, and if the random number generation algorithm used has not changed since Aaron audited the code on June 20, 2020, then the value of “Yes” in the “CRNG” column of the spreadsheet tells you that this tool uses a cryptographically secure random number generator; likewise, a “Yes” in the “Uniform” column indicates that the random number distribution is uniform. This is explained in Aaron’s blog article about the Password Generator Audit.
If you trust the creators of the Little Password Helper tool, you can read what they have to say about the random number generation in their FAQ:
How’s the RNG work? In the browser: with WebCrypto, specifically with
getRandomValues. In NodeJS: withcrypto.randomBytes.
If you trust neither, have a look at the source code:
Don’t rely on password strength testers. In this case, it is more accurate (and easier) to compute the entropy by knowing that the word list used by the Little Password Helper contains 11,501 words. Thus, in a random passphrase generated by this tool, each word contributes 13.5 bits of entropy. A four-word passphrase would have 54 bits of entropy, which is sufficient for the master password of a Bitwarden vault.
If you need a random passphrase with higher entropy (for example, if it will be used as the basis for cryptographic key generation using a fast key derivation function such as MD5 or NTLM), then you need additional words. To surpass 128 bits of entropy, you would need 10 words.
Thanks for your very thoughtful responses, grb, I really appreciate that!
Ah, the “bad” Math.random was in my browser extensions (further investigation for another day). My first time doing such a deep dive with browser dev tools.
As promised by the creators, here is the RNG call in my copy of the Little Password Helper:
return "object" == typeof window.crypto && "function" == typeof window.crypto.getRandomValues ? function(e, a) {
So that’s good. Using dev tools breakpoints, I could see LPH hit that line on page reload, and could see the values it was collecting.
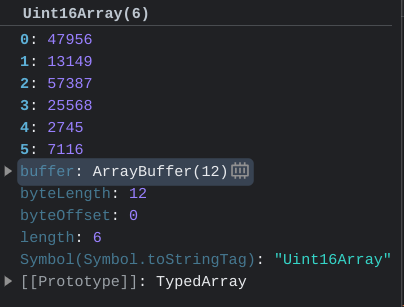
It looks like LPH returns
r = Uint16Array(6)
where each of the 6 array elements holds 2 bytes; 62=12 bytes, 128=96 bits.
I know hardly anything about any of this, so I’m likely barking at the moon, but Aaron’s blog seems to expect UInt32Array (“32”, not LPH’s “16”), and the spreadsheet has an “80” in the Entropy column (not 96).
I guess 96 is a lot, but I think I wish it was 128.
(I’m obsessing over this because of last month’s libbitcoin-explorer bx milksad debacle, and the pain I suffered with the 2008 debian openssl debacle.)
Thanks again, grb!
PS: I like your avatar.
You’re definitely overthinking. Aaron’s mention of the uint32 data type was only an example, not a prescription. I am not going to reverse engineer the LPH source code to prove that it produces uniformly distributed, cryptographically secure random numbers; Aaron has already done this, and I trust his work.
As for entropy, I already did the analysis above. Each word produces 13.5 (well, 13.4895 or so) bits of entropy, and the “RNG Entropy” section of Aaron’s blog article explains that he evaluated the entropy for the default passphrase size produced by the tool. In the case of the LHP site, the default length is 6 words, so 6×13.4895 = 80.937, which he has rounded down to 80 bits.
If you want more entropy, you don’t need a different random number generator, you just need to increase the number of words in your passphrase. As I already pointed out in my previous response, to get 128 bits of entropy, you just need to generate a passphrase containing 10 words (which will have almost 135 bits of entropy). A 19-word passphrase generated by the LPH will have just over 256 bits of entropy.
The entropy per word is directly related to the length of the word list used by the generator, so if you need passphrases with a high level of entropy, you may also want to consider the Niceware generator, which produces 16 bits of entropy per word (thus, you’d only need 8 words to get 128 bits of entropy).
P.S. Героям слава!
now if we could just get niceware in navaho, they’ll never break it ![]()
Aaron’s own passphrase generator will do Klingon and Elvish, among others.