Hello Bitwarden Community!
I’m Kevin, the new Director of Product Design at Bitwarden. I joined Bitwarden late last year, and I’m thrilled to join this amazing community and team.
My Background
With 16 years of experience in product design, I specialize in gathering user insights and turning them into delightful solutions. I love learning about users to create products that solve real problems.
Exciting Improvements Coming
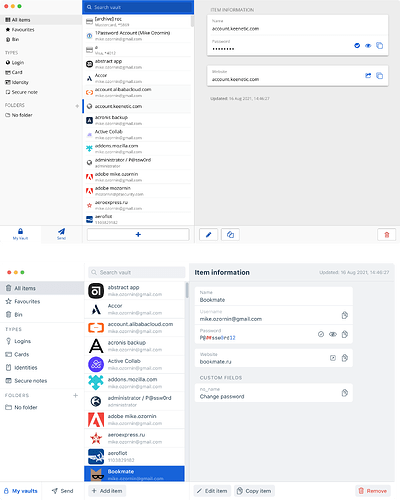
We have been listening closely to your feedback on improving Bitwarden’s user experience. Thank you for the creativity and passion you’ve shared - it’s very insightful. We’re now working on a project to improve Bitwarden’s UX, making securing your passwords, passkeys, and sensitive information even better.
We Need Your Help
We believe the best way to enhance Bitwarden is by collaborating with you, our users. We want to hear what you love and what needs improving. Your perspectives will directly guide our design process.
Become a Bitwarden Product Tester
I’m inviting you to join our user research program and get hands-on with our new UX. You’ll get an exclusive peek at what we’re building and can share candid feedback to help us create the best product possible. It’s easy to sign up via this Google Form link or this CryptPad link. We welcome both new and existing users from all backgrounds.
We’re committed to building the best experience we can for you. Please reach out in the comments - I look forward to your thoughts and to working together!