I run a small software development company, and we are testing BitWarden for a client as a potential replacement for another popular secure password manager.
So far we have had very good feedback, except for one very concerning item: about 7% of their users reported that URL matching fails, only for one specific website (the same site for all of those users, across different devices and device types).
This concerns these users because the site is controversial, and the fact that the same site fails login matching for all of them—on different device types—points to this being a URL blocking issue rather than a technical issue. (Indeed, other of our test users consider the site objectionable.)
The big question this raises is: Can BitWarden apply filtering to the URLs in a user’s vault (and by extension, see / record / catalog them)? I had assured this prospective client that the contents of users’ vaults were entirely opaque to BitWarden, and that all functionality happened on the client, rather than the server. If multiple users find the same objectionable site being excluded from matching by the client, then this seems to represent a somewhat severe security hole, in that BitWarden has the capability to interdict and interfere with the their utility’s functionality based on concerns of third parties, i.e., the utility is not fully under users’ control, nor is their data truly private.
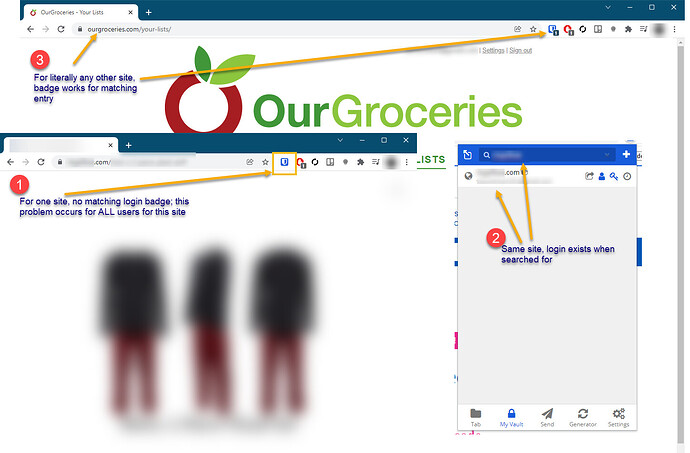
I will try to include screenshots of the issue here. Basically, 1) the matching login functionality fails for this (and only this) site, 2) the site can be found in each user’s vault by searching, and 3) URL matching does not fail for any other site.
Please note that the issue here has nothing to do with anyone’s judgement call about the objectionability of the destination site. This is exclusively about whether there is a security hole in BitWarden which would allow malicious insiders to observe what URLs are in users’ vaults and selectively conceal matching logins from some/any of them.
Can anyone here help me figure out how to prove to this client that BitWarden has no control over or visibility into the URLs in people’s vaults? If the vault is encrypted and all functionality happens on the client rather than the server, the app failures they’re seeing should be impossible. If I was wrong about that, I feel humiliated for suggesting this software/service as an enterprise solution. As a human being, I can consider certain content objectionable, but as a security professional, I cannot recommend any utility that has any ability to apply the provider’s editorial preferences to users’ experience with the product.
Thanks!