Docker and bitwarden is installed..
normally when I enter https://tivi.selfdhost.me in my browser, bitwarden has to come, but I get the internal friztbox page ???
Hello @vin0t ,
I have two suggestions:
- Try the Ip address where the bitwarden is running directly.
- Check at which port bitwarden is running and add that accordingly (ex. 192.168.1.100:8443)
Hi Pulsar,
How can I find my IP and port?
is ony bwdata /nginx/default.conf but not nginx-conf
Hello @vin0t,
To find your ip simply run ip addr on linux and on windows ipconfig.
For the port, search under bwdata/docker for docker-compose.yml. On the compose file search for port, you should normaly see:
ports:
- '80:8080'
- '443:8443'
Note: there is also a docker-compose.override.yml file. This one overrides the above. Please search there if there are ports overriden, example:
ports:
- '8000:8080'
- '443:8443'
In that case your non TLS port would be 8000 and TLS port is 443 (which is simply accessed with https://<IP-ADDRESS>
If you are running it on your PC directly you can simply type:
localhost:8000
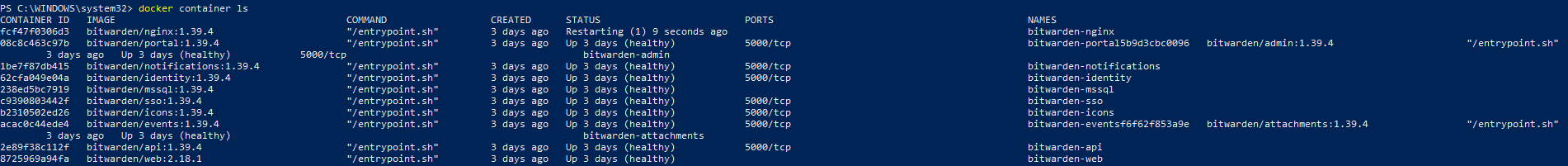
PS: There is an easier way: docker container ls and search for bitwarden/nginx and look at the ports  , but I think the information above is useful.
, but I think the information above is useful.
Hope this helps 
Hi Pulsar,
“docker container ls” → Something is wrong here, the port cannot be seen
The file bwdata / docker for docker-compose.yml is there, but
the file bwdata / docker for docker-compose.overrider.yml does not exist.
It seems that bitwarden-nginx container is not functioning properly (Restarting). Check out the logs by running docker-compose logs -f | grep "nginx" under the folder where docker-compose.yml file is.
my docker-compose.yml
identity:
image: bitwarden/identity:1.39.4
container_name: bitwarden-identity
restart: always
volumes:
- ../identity:/etc/bitwarden/identity
- ../core:/etc/bitwarden/core
- ../ca-certificates:/etc/bitwarden/ca-certificates
- ../logs/identity:/etc/bitwarden/logs
env_file:
- global.env
- ../env/uid.env
- ../env/global.override.env
networks:
- default
- public
sso:
image: bitwarden/sso:1.39.4
container_name: bitwarden-sso
restart: always
volumes:
- ../identity:/etc/bitwarden/identity
- ../core:/etc/bitwarden/core
- ../ca-certificates:/etc/bitwarden/ca-certificates
- ../logs/sso:/etc/bitwarden/logs
env_file:
- global.env
- ../env/uid.env
- ../env/global.override.env
networks:
- default
- public
admin:
image: bitwarden/admin:1.39.4
container_name: bitwarden-admin
restart: always
depends_on:
- mssql
volumes:
- ../core:/etc/bitwarden/core
- ../ca-certificates:/etc/bitwarden/ca-certificates
- ../logs/admin:/etc/bitwarden/logs
env_file:
- global.env
- ../env/uid.env
- ../env/global.override.env
networks:
- default
- public
icons:
image: bitwarden/icons:1.39.4
container_name: bitwarden-icons
restart: always
volumes:
- ../ca-certificates:/etc/bitwarden/ca-certificates
- ../logs/icons:/etc/bitwarden/logs
env_file:
- global.env
- ../env/uid.env
networks:
- default
- public
notifications:
image: bitwarden/notifications:1.39.4
container_name: bitwarden-notifications
restart: always
volumes:
- ../ca-certificates:/etc/bitwarden/ca-certificates
- ../logs/notifications:/etc/bitwarden/logs
env_file:
- global.env
- ../env/uid.env
- ../env/global.override.env
networks:
- default
- public
events:
image: bitwarden/events:1.39.4
container_name: bitwarden-events
restart: always
volumes:
- ../ca-certificates:/etc/bitwarden/ca-certificates
- ../logs/events:/etc/bitwarden/logs
env_file:
- global.env
- ../env/uid.env
- ../env/global.override.env
networks:
- default
- public
nginx:
image: bitwarden/nginx:1.39.4
container_name: bitwarden-nginx
restart: always
depends_on:
- web
- admin
- api
- identity
ports:
- '8000:8080'
- '443:8443'
volumes:
- ../nginx:/etc/bitwarden/nginx
- ../letsencrypt:/etc/letsencrypt
- ../ssl:/etc/ssl
- ../logs/nginx:/var/log/nginx
env_file:
- ../env/uid.env
networks:
- default
- public
networks:
default:
internal: true
public:
internal: falseThere should be two certificates (fullchain.pem, key.**pem) for bitwarden in any of these folders:
../nginx
../letsencrypt
../ssl
which they should be under bwdata.
Sorry I just forgot that you are using windows, try this and it should give you logs from nginx container that is not running properly:
docker-compose logs bitwarden-nginx
or check the directory
../logs/nginx /* From docker-compose.yml file */
Hope this helps ![]()
Sorry I just forgot that you are using windows, try this and it should give you logs from nginx container that is not running properly:
docker-compose logs bitwarden-nginx
![]()
logs:
2021/02/12 18:50:31 [emerg] 1#1: cannot load certificate “/etc/letsencrypt/live/tivi.selfhost.me/fullchain.pem”: BIO_new_file() failed (SSL: error:02001002:system library:fopen:No such file or directory:fopen(’/etc/letsencrypt/live/tivi.selfhost.me/fullchain.pem’,‘r’) error:2006D080:BIO routines:BIO_new_file:no such file)
Hi Pulsar,
my docker ps -a ![]()
when I enter https://tivi.selfdhost.me in my browser, bitwarden has to come, but I get the internal friztbox page ???
Hello @vin0t,
That looks good, how did you fix the problem?
Before trying directly your link, try first to access it directly http://localhost and https://localhost
For the domain, I have some questions:
- Are you hosting bitwarden on a local computer?
- Do you want to access it from other devices in your local network?
Hi Pulsar,
That looks good, how did you fix the problem?
->Windows>System32>bwdata>nginx war just “default.conf”; duplicate the file and rename it to nginx.conf.
Problems:
Before trying directly your link, try first to access it directly http://localhost and https://localhost
http://localhost → This page is not working localhost did not send any data.
ERR_EMPTY_RESPONSE
https://localhost->The website is unreachable localhost has unexpectedly closed the connection.
Try the following:
Check connection
Check proxy and firewall
Run Windows Network Diagnostics
ERR_CONNECTION_CLOSED
why???
Hi @vin0t,
strange, did you try 127.0.0.1:80, and 127.0.0.1:443 ?
If they are not working, is maybe the firewall blocking it?
Check out my nginx configuration, ${BW_HOST} is the hostname (ex. vault.example.com) and ${BW_TLS_PATH} is the path for the TLS certificates.
#######################################################################
# WARNING: This file is generated. Do not make changes to this file. #
# They will be overwritten on update. You can manage various settings #
# used in this file from the ./bwdata/config.yml file for your #
# installation. #
#######################################################################
server {
listen 8080 default_server;
listen [::]:8080 default_server;
server_name ${BW_HOST};
return 301 https://${BW_HOST}$request_uri;
}
server {
listen 8443 ssl http2;
listen [::]:8443 ssl http2;
server_name ${BW_HOST};
ssl_certificate ${BW_TLS_PATH}/${BW_HOST}/fullchain.pem;
ssl_certificate_key ${BW_TLS_PATH}/${BW_HOST}/key.pem;
ssl_session_timeout 30m;
ssl_session_cache shared:SSL:20m;
ssl_session_tickets off;
# Diffie-Hellman parameter for DHE ciphersuites, recommended 2048 bits
ssl_dhparam ${BW_TLS_PATH}/dhparam.pem;
ssl_protocols TLSv1.2;
ssl_ciphers "ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-CHACHA20-POLY1305:ECDHE-RSA-CHACHA20-POLY1305:ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES256-SHA384:ECDHE-RSA-AES256-SHA384:ECDHE-ECDSA-AES128-SHA256:ECDHE-RSA-AES128-SHA256";
# Enables server-side protection from BEAST attacks
ssl_prefer_server_ciphers on;
# OCSP Stapling ---
# Fetch OCSP records from URL in ssl_certificate and cache them
ssl_stapling on;
ssl_stapling_verify on;
# Verify chain of trust of OCSP response using Root CA and Intermediate certs
ssl_trusted_certificate ${BW_TLS_PATH}/${BW_HOST}/fullchain.pem;
resolver 1.1.1.1 1.0.0.1 9.9.9.9 149.112.112.112 valid=300s;
include /etc/nginx/security-headers-ssl.conf;
include /etc/nginx/security-headers.conf;
location / {
proxy_pass http://web:5000/;
include /etc/nginx/security-headers-ssl.conf;
include /etc/nginx/security-headers.conf;
add_header Content-Security-Policy "default-src 'self'; style-src 'self' 'unsafe-inline'; img-src 'self' data: https://haveibeenpwned.com https://www.gravatar.com; child-src 'self' https://*.duosecurity.com; frame-src 'self' https://*.duosecurity.com; connect-src 'self' wss://${BW_HOST} https://api.pwnedpasswords.com https://twofactorauth.org; object-src 'self' blob:;";
add_header X-Frame-Options SAMEORIGIN;
add_header X-Robots-Tag "noindex, nofollow";
}
location /alive {
return 200 'alive';
add_header Content-Type text/plain;
}
location = /app-id.json {
proxy_pass http://web:5000/app-id.json;
include /etc/nginx/security-headers-ssl.conf;
include /etc/nginx/security-headers.conf;
proxy_hide_header Content-Type;
add_header Content-Type $fido_content_type;
}
location = /duo-connector.html {
proxy_pass http://web:5000/duo-connector.html;
}
location = /u2f-connector.html {
proxy_pass http://web:5000/u2f-connector.html;
}
location /attachments/ {
proxy_pass http://attachments:5000/;
}
location /api/ {
proxy_pass http://api:5000/;
}
location /identity/ {
proxy_pass http://identity:5000/;
}
location /icons/ {
proxy_pass http://icons:5000/;
}
location /notifications/ {
proxy_pass http://notifications:5000/;
}
location /notifications/hub {
proxy_pass http://notifications:5000/hub;
proxy_set_header Upgrade $http_upgrade;
proxy_set_header Connection $http_connection;
}
location /events/ {
proxy_pass http://events:5000/;
}
location /admin {
proxy_pass http://admin:5000;
include /etc/nginx/security-headers-ssl.conf;
include /etc/nginx/security-headers.conf;
add_header X-Frame-Options SAMEORIGIN;
}
}
Hope this helps 
Hello @vin0t,
did you manage to get it to work? Sadly it is a little bit difficult for me to help you as I have limited view of what is actually happening. When I find the time, I will recreate your situation in a windows environment and find out what possible problems are there.
Cheers
Hi Pulsar,
wie geht ?
Habe nun QNAP TS-x53D mit Virtualisierung (Ubuntu 20.4) und Bitwarden auf Terminal installiert.
Es scheint zu funktionieren. Nun möchte ich die Daten local behalten.
Wie ?