They are exactly same as software but are sealed so you cannot backup the secret in them. If you lose the token that is it. They are also not vulnerable to virus since they are sealed
I currently use Bitwarden Free, protected by Authy (the best 2FA App I could find) , Bitwarden should email us in case our master password is inserted and TOTP is mistakenly inserted consecutively, so that we know if someone is trying to brute force and change the master password immediately to rebuild to First line of defense
So is the Unicredit pass safer than the Unicredit app?
Thanks so much!
Litero
Interesting, I did not know that the hardware token provide additional protection for transactions. I am curious about the following then.
- Is the implementation the same across banks? Do all banks provide the level of protection you indicated or does implementation vary from bank to bank?
- Does the system prompt you for a token on a transaction? You mentioned that you have to enter the token in addition to the value.
- Have you heard if there are flaws on token recovery procedure or when user “loses” their token. Note that this may be specific to banks, but I recall one user complaining that they could bypass the token by calling the bank and getting a temp password to bypass the token.
Thanks for the info!
Banksters assuming that everyone has a phone and wishes to use it for banking is a problem in itself.
While I an content to use a computer for online banking, the idea of using a phone contraption, which is less secure than my computer and has a ridiculously small screen is not something the Banksters are going to convince me about anytime soon.
My Yubikeys will do challenge-response and the antipathy of Banksters towards them is beyond my understanding.
Banks are usually really conservative and do not like to adopt new technology. They are more concern with usability than security. They are not entirely wrong. If you implement additional security, they will get an increase in number of angry customer and increase support calls which cost them money. They will adopt the technology once the practice become more common place so that people are more comfortable using the new technology and they start looking behind the times or they start losing money due to hacks.
Some banks offer the possibility to access the online internet banking account, only in information mode and as an additional option also in disposition mode.
Should I be more secure if I subscribe to an internet banking contract only in information mode?
Thanks so much!
Yes and no.
No matter how SMS or push notification is used the customer has to check that what they think they have input is correct, the amount and account details. There can be some automated checking of the details, but the amount cannot be totally checked (other than whether it is within the agreed limits of the account it is being sent from). In other words this information is fed back tot he customer for checking.
SMS is extremely insecure and can be interfered with, so should not be used for anything important in my view. Push-notification is less susceptible to interference than SMS, but it can be interfered with. Both can be interfered with, so both the checking messages sent back to the customer can be interfered with. Thus the customer can be told that the funds are to be dent to account number X, but they are actually to be sent to account Y. Banksters assert that their systems are perfect and thus the responsibility for such a transfer would lie with the customer.
Now a Yubikey (4 or 5) can undertake a number of functions which make such attacks much more difficult.
I agree on your first point.
I disagree on your second point. Security keys are far easier to use than mobile phone contraptions. There isn’t a battery, software and other gubbins to fail. A security key does a small number of things well, a phone contraption does many things averagely. If banksters had any sense they would realise that security keys would reduce the number of angry customers, because there is a lot less to go wrong than with phone contraptions.
I use a security key to login to Bitwarden because, as well as being the most secure method, it is also the fastest (infinitely faster than taking out my phone contraption, calling up Authy, looking at the right TOTP dispaly and keying he numbers into the computer). Banksters appear to still be stuck in the late 20th Century, when mobile phone contraptions were new.
When I first thought of this question, I kind of meant leaks involving technical stuff: Encrypted Bitwarden Databases with key or without key get leaked? (Does the AES-CBC key get leaked?) so that I could lead to another question: If a malicious actor knows your password but not your 2FA, is it safe to not rotate your encryption key?
Assuming Master Passwords were derived from 100,000+ rounds of PBKDF2 SHA-256, if a local attacker determines the correct password via any Bitwarden Login Portal. He/she could’ve run PBKDF2 and derive AES-CBC secret key for the encrypted vault themselves, assuming PBKDF2 rounds parameter get sent back when the correct password is entered (without 2FA). Herein lies the obscurity of what does the attackers without 2FA really know? Encrypted Vault? PBKDF2 parameters?
Some banks also provide push notification or alternatively their own TOTP app: which of the two is more secure?
Thanks so much!
It probably depends if the app that receives the push notification or the other app that provides the TOTP is more secure. You as a user only have very limited options to find out about this. Go to the store for your smartphone, take a look at both apps and find out if at least one of them still receives updates. If it is only one of them, take that app. If both still receive updates install both and then keep the one that makes you feel better about it.
For what I can see from your replies you are looking for the perfect and 100% secure solution. This does not exist. However using any password manager already makes you a very difficult target. Most of the population does not use one. See here and remember that this is just about los gringos; in a lot of other countries probably even less people use a password manager. And a lot of users of password managers do not use it the way they should. They only use it as some kind of a backup for their memory. That means that they either have some kind of a rule for their passwords or keep on using the same password(s) again and again. Instead they should make use of the capabilities a password manager offers: Create long complicated and unique passwords for every single account: Definitely have them much longer than 10 characters, with a random mixture of upper and lower case characters, numbers and special characters.
Your only concerns should be: Where do I have a copy of the password for my password manager?
And: Do I have a reliable backup?
TL;DR: Unless some government is trying to get all your data it is are safe if you use a password manager and actually make use of its capabilities.
Pippo
Depending on implementation, the bank push notification can theoretically be more secure than the TOTP. The reason is that TOTP can be brute force. If they implement push notification properly, it would be using the TPM on a smartphone which would mean it’s equivalent to a Yubikey. This is the principle behind google prompt.
Again, pay more attention to how the account handle the recovery. In most cases TOTP is probably effective but a lot of account are implemented badly which may allow an account bypass anything 2FA.
The push up notification and the other mobile token (TOPT) option are handled by the same app that the bank provides:
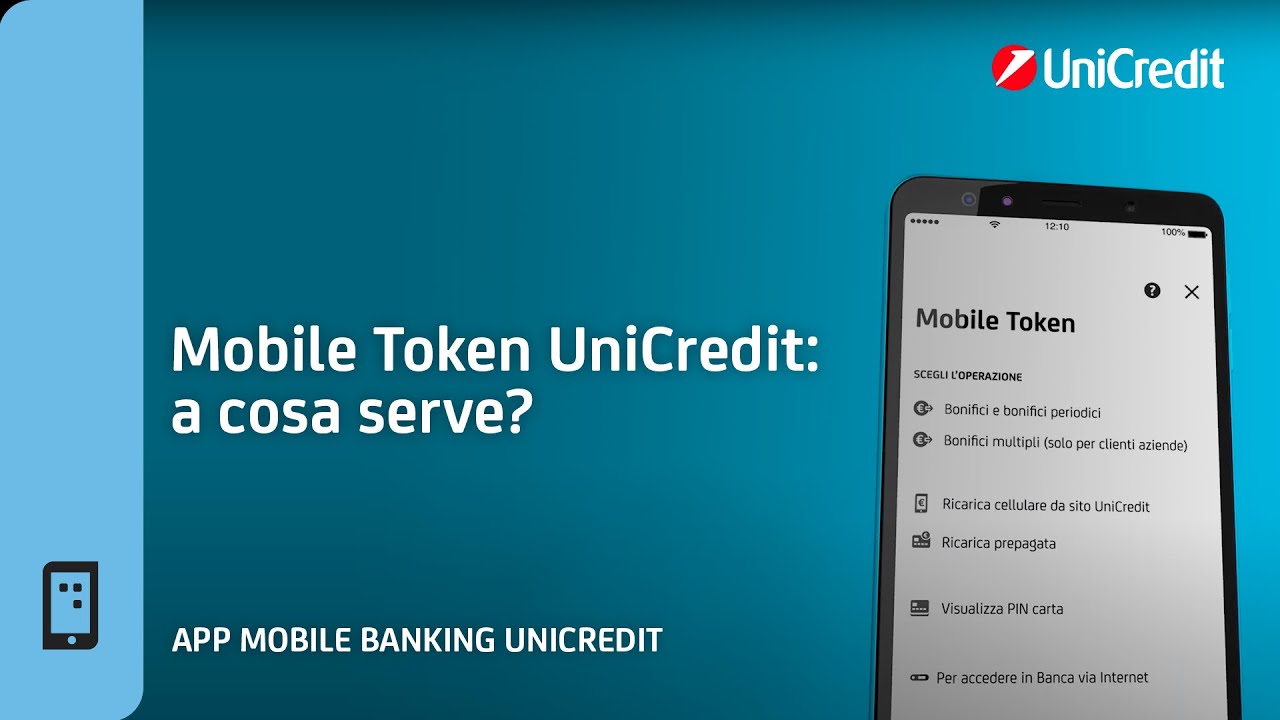
The mobile token first requires an access mpin (which is not required with the push up notification) and then subsequently generates the code to authorize the transition:
Thanks so much!